Database Access with AWS RDS Proxy for Microsoft SQL Server
Teleport can provide secure access to Amazon RDS proxy for Microsoft SQL Server via the Teleport Database Service. This allows for fine-grained access control through Teleport's RBAC.
In this guide, you will:
- Configure your Amazon RDS proxy for Microsoft SQL Server database with IAM authentication.
- Add the database to your Teleport cluster.
- Connect to the database via Teleport.
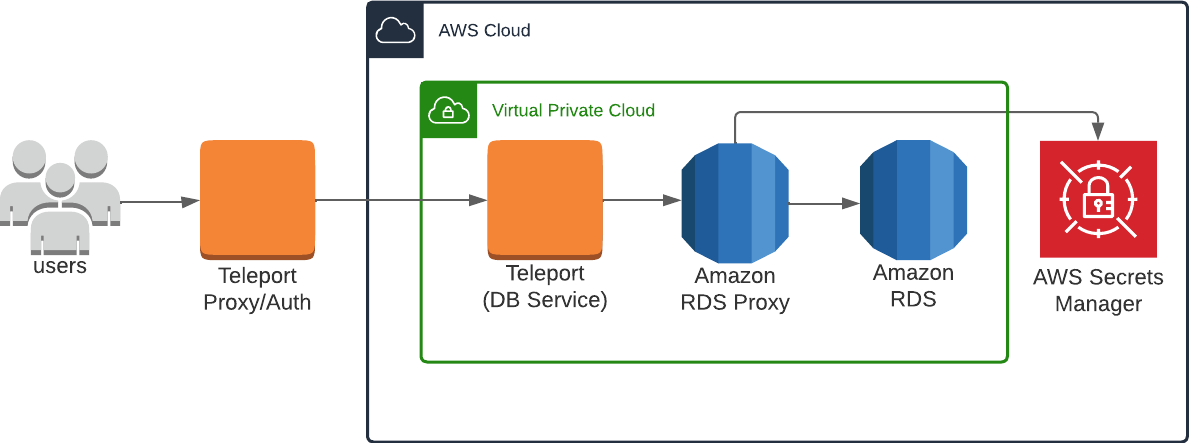
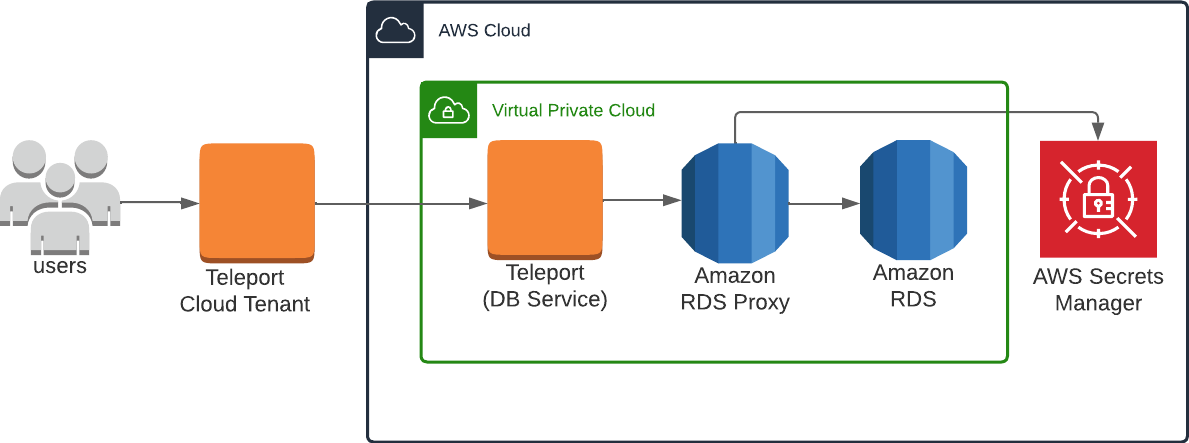
How it works
The Teleport Database Service uses IAM authentication to communicate with RDS Proxy. When a user connects to the database via Teleport, the Teleport Database Service obtains AWS credentials and authenticates to AWS as an IAM principal with permissions to manage the database.
- Self-Hosted
- Cloud-Hosted
Teleport currently supports RDS Proxy instances with engine family PostgreSQL, MariaDB/MySQL or Microsoft SQL Server.
This guide shows how to register a single RDS Proxy with your Teleport cluster. For a more scalable approach, learn how to set up Database Auto-Discovery to automatically enroll all AWS databases in your infrastructure.
Prerequisites
-
A running Teleport cluster version 15.4.22 or above. If you want to get started with Teleport, sign up for a free trial or set up a demo environment.
-
The
tctladmin tool andtshclient tool.On Teleport Enterprise, you must use the Enterprise version of
tctl, which you can download from your Teleport account workspace. Otherwise, visit Installation for instructions on downloadingtctlandtshfor Teleport Community Edition.
- AWS account with RDS Proxy instances and permissions to create and attach IAM policies.
- Any RDS Proxy instances intended for connection through Teleport must have TLS enabled.
- A host, e.g., an EC2 instance, where you will run the Teleport Database Service.
- To check that you can connect to your Teleport cluster, sign in with
tsh login, then verify that you can runtctlcommands using your current credentials.tctlis supported on macOS and Linux machines. For example:If you can connect to the cluster and run the$ tsh login --proxy=teleport.example.com --user=email@example.com
$ tctl status
# Cluster teleport.example.com
# Version 15.4.22
# CA pin sha256:abdc1245efgh5678abdc1245efgh5678abdc1245efgh5678abdc1245efgh5678tctl statuscommand, you can use your current credentials to run subsequenttctlcommands from your workstation. If you host your own Teleport cluster, you can also runtctlcommands on the computer that hosts the Teleport Auth Service for full permissions.
Step 1/7. Install Teleport
Install Teleport on your Linux server:
-
Assign edition to one of the following, depending on your Teleport edition:
Edition Value Teleport Enterprise Cloud cloudTeleport Enterprise (Self-Hosted) enterpriseTeleport Community Edition oss -
Get the version of Teleport to install. If you have automatic agent updates enabled in your cluster, query the latest Teleport version that is compatible with the updater:
$ TELEPORT_DOMAIN=example.teleport.com
$ TELEPORT_VERSION="$(curl https://$TELEPORT_DOMAIN/v1/webapi/automaticupgrades/channel/default/version | sed 's/v//')"Otherwise, get the version of your Teleport cluster:
$ TELEPORT_DOMAIN=example.teleport.com
$ TELEPORT_VERSION="$(curl https://$TELEPORT_DOMAIN/v1/webapi/ping | jq -r '.server_version')" -
Install Teleport on your Linux server:
$ curl https://cdn.teleport.dev/install-v15.4.22.sh | bash -s ${TELEPORT_VERSION} editionThe installation script detects the package manager on your Linux server and uses it to install Teleport binaries. To customize your installation, learn about the Teleport package repositories in the installation guide.
Step 2/7. Create a Teleport Database Service configuration
The Database Service requires a valid join token to join your Teleport cluster.
Run the following tctl command and save the token output in /tmp/token
on the server that will run the Database Service:
$ tctl tokens add --type=db --format=text
abcd123-insecure-do-not-use-this
Alternative methods
For users with a lot of infrastructure in AWS, or who might create or recreate many instances, consider alternative methods for joining new EC2 instances running Teleport:
Create the Database Service configuration. Replace teleport.example.com:443 with the domain name and port of your Teleport Proxy Service or cloud-hosted Teleport Enterprise account and endpoint:port with the host and port of the database endpoint:
$ sudo teleport db configure create \
-o file \
--proxy=teleport.example.com:443 \
--uri=endpoint:port \
--protocol=sqlserver \
--token=/tmp/token \
--labels=env=dev
The command will generate a Teleport Database Service configuration file and
place it at the /etc/teleport.yaml location.
Step 3/7. Configure AWS Credentials
Grant the Teleport Database Service access to credentials that it can use to authenticate to AWS. If you are running the Teleport Database Service on an EC2 instance, you may use the EC2 Instance Metadata Service method. Otherwise, you must use environment variables:
- Instance Metadata Service
- Environment Variables
Teleport will detect when it is running on an EC2 instance and use the Instance Metadata Service to fetch credentials.
The EC2 instance should be configured to use an EC2 instance profile. For more information, see: Using Instance Profiles.
Teleport's built-in AWS client reads credentials from the following environment variables:
AWS_ACCESS_KEY_IDAWS_SECRET_ACCESS_KEYAWS_DEFAULT_REGION
When you start the Teleport Database Service, the service reads environment variables from a
file at the path /etc/default/teleport. Obtain these credentials from your
organization. Ensure that /etc/default/teleport has the following content,
replacing the values of each variable:
AWS_ACCESS_KEY_ID=00000000000000000000
AWS_SECRET_ACCESS_KEY=0000000000000000000000000000000000000000
AWS_DEFAULT_REGION=<YOUR_REGION>
Have multiple sources of AWS credentials?
Teleport's AWS client loads credentials from different sources in the following order:
- Environment Variables
- Shared credentials file
- Shared configuration file (Teleport always enables shared configuration)
- EC2 Instance Metadata (credentials only)
While you can provide AWS credentials via a shared credentials file or shared
configuration file, you will need to run the Teleport Database Service with the AWS_PROFILE
environment variable assigned to the name of your profile of choice.
If you have a specific use case that the instructions above do not account for, consult the documentation for the AWS SDK for Go for a detailed description of credential loading behavior.
Step 4/7. Create an IAM policy for Teleport
Teleport needs AWS IAM permissions to be able to access RDS Proxy instances.
Teleport can bootstrap IAM permissions for the Database Service based on its
configuration using the teleport db configure bootstrap command. You can use
this command in automatic or manual mode:
- In automatic mode, Teleport will attempt to create appropriate IAM policies and attach them to the specified IAM identity role. This requires IAM permissions to create and attach IAM policies.
- In manual mode, Teleport will print required IAM policies. You can then create and attach them manually using the AWS management console.
- Automatic IAM setup
- Manual IAM setup
Use this command to bootstrap the permissions automatically when your Teleport Database Service runs as an IAM role (for example, on an EC2 instance with an attached IAM role).
$ teleport db configure bootstrap -c /etc/teleport.yaml --attach-to-role TeleportRole
Use this command to display required IAM policies which you will then create in your AWS console:
$ teleport db configure bootstrap -c /etc/teleport.yaml --manual --attach-to-role arn:aws:iam::123456789012:role/TeleportRole
Bootstrapping with assume_role_arn in config
When assume_role_arn is configured for databases or AWS matchers,
teleport db configure bootstrap will determine permissions required for the
bootstrap target AWS IAM identity using the following logic:
- When the target does not match
assume_role_arnin any database resource or AWS matcher in the configuration file, the target is assumed to be the Teleport Database Service's AWS IAM identity and permissions are bootstrapped for all the configured static databases and AWS matchers. - When an
--attach-to-roletarget matches anassume_role_arnsetting for static databases or AWS matchers in the configuration file, permissions will be bootstrapped only for those static databases or AWS matchers.
You will need to run the bootstrap command once with the Teleport Database
Service's IAM identity as the policy attachment target, and once for each AWS
IAM role that is used for assume_role_arn.
Step 5/7. Start the Database Service
Configure the Teleport Database Service to start automatically when the host boots up by creating a systemd service for it. The instructions depend on how you installed the Teleport Database Service.
- Package Manager
- TAR Archive
On the host where you will run the Teleport Database Service, enable and start Teleport:
$ sudo systemctl enable teleport
$ sudo systemctl start teleport
On the host where you will run the Teleport Database Service, create a systemd service configuration for Teleport, enable the Teleport service, and start Teleport:
$ sudo teleport install systemd -o /etc/systemd/system/teleport.service
$ sudo systemctl enable teleport
$ sudo systemctl start teleport
You can check the status of the Teleport Database Service with systemctl status teleport
and view its logs with journalctl -fu teleport.
Step 6/7. Configure database user credentials
The Database Service connects to an RDS Proxy instance using IAM authentication. In addition, the RDS Proxy instance must also be able to connect to the RDS DB instance or Aurora DB cluster using pre-configured database user credentials.
First, use Secrets Manager to store sets of user name and password credentials. You create a separate Secrets Manager secret for each database user account that RDS Proxy connects to on the RDS DB instance or Aurora DB cluster. The password associated with the secret must match the database password for that user in the target database.
For example, the following AWS CLI command creates a Secrets Manager secret for
database user alice:
$ aws secretsmanager create-secret \
--name rdsproxy_alice --description "database user alice" \
--secret-string '{"username":"alice","password":"password_for_alice"}'
Next, create an IAM role with a policy that can access these secrets, for example:
{
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Action": "secretsmanager:GetSecretValue",
"Resource": [
"arn:aws:secretsmanager:us-west-1:account_id:secret:rdsproxy_alice",
"arn:aws:secretsmanager:us-west-1:account_id:secret:rdsproxy_anotheruser"
]
},
{
"Effect": "Allow",
"Action": "kms:Decrypt",
"Resource": "arn:aws:kms:us-west-1:account_id:key/key_id",
"Condition": {
"StringEquals": {
"kms:ViaService": "secretsmanager.us-east-2.amazonaws.com"
}
}
}
]
}
The IAM role should have the following trust policy:
{
"Version": "2012-10-17",
"Statement": [
{
"Sid": "",
"Effect": "Allow",
"Principal": {
"Service": "rds.amazonaws.com"
},
"Action": "sts:AssumeRole"
}
]
}
Lastly, modify the RDS Proxy authentication settings to use the created IAM role and Secrets Manager secrets. Make sure IAM authentication is set to Required:
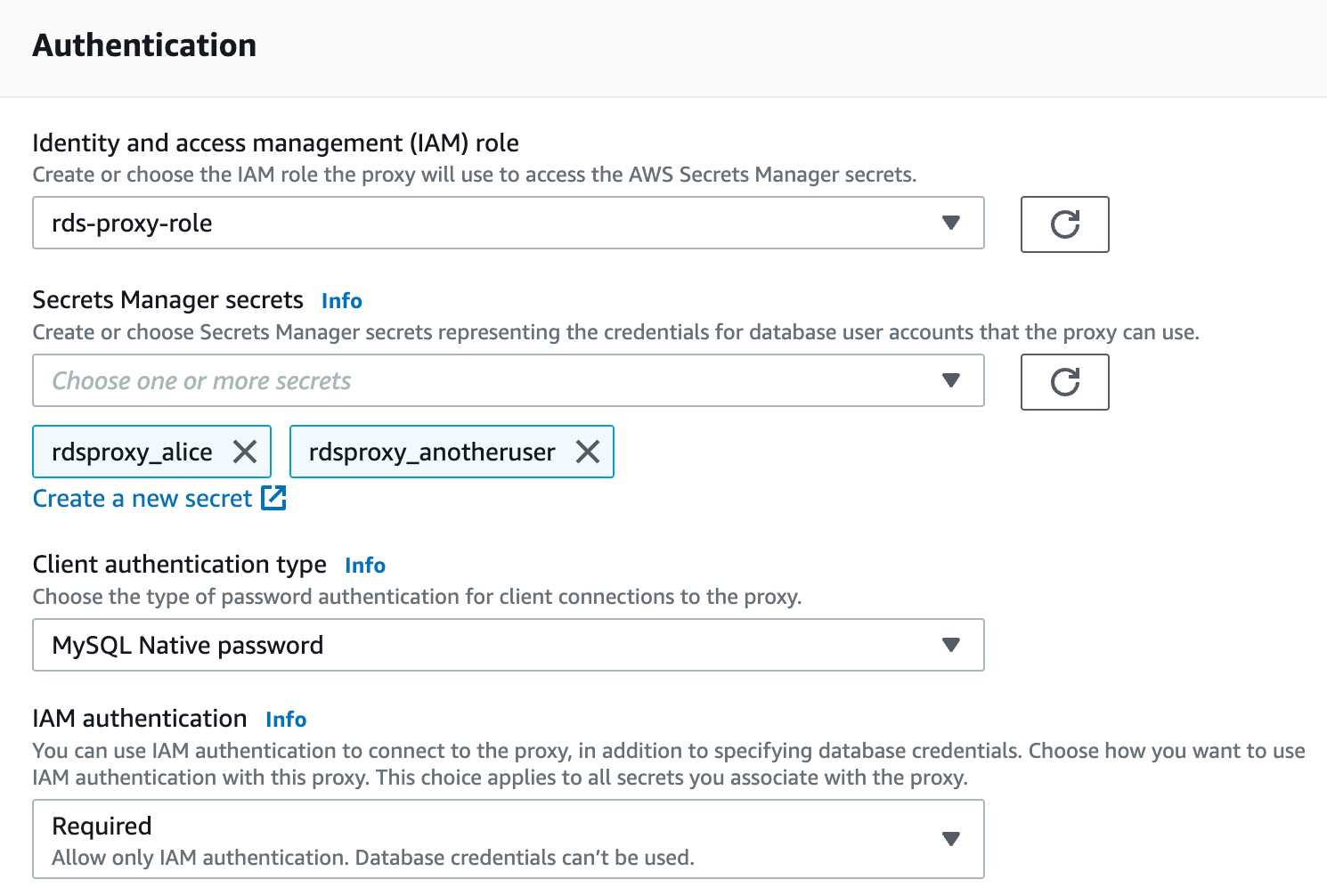
If you need to disable IAM authentication for some database users that are not intended for Teleport access, use the following AWS CLI command to set IAMAuth per secret:
$ aws rds modify-db-proxy --db-proxy-name my-rds-proxy --auth AuthScheme=SECRETS,SecretArn=arn-of-teleport-access-user,\
IAMAuth=REQUIRED AuthScheme=SECRETS,SecretArn=arn-of-non-teleport-user,IAMAuth=DISABLED ...
See aws rds modify-db-proxy help for more information.
Step 7/7. Connect
Once the Database Service has started and joined the cluster, log in to see the registered database:
$ tsh login --proxy=teleport.example.com:443 --user=alice
$ tsh db ls
Name Description Labels
---------------------------- ------------------------------- -------
rds-proxy RDS Proxy in us-west-1 ...
Retrieve credentials for the database and connect to it as the alice user:
$ tsh db connect --db-user=alice --db-name=dev rds-proxy
To log out of the database and remove credentials:
$ tsh db logout rds-proxy
Troubleshooting
Certificate error
If your tsh db connect error includes the following text, you likely have an RDS database created before July 28, 2020, which presents an X.509 certificate that is incompatible with Teleport:
x509: certificate relies on legacy Common Name field, use SANs instead
AWS provides instructions to rotate your SSL/TLS certificate.
No credential providers error
If you see the error NoCredentialProviders: no valid providers in chain in Database Service logs then Teleport
is not detecting the required credentials to connect via AWS IAM permissions. Check whether
the credentials or security role has been applied in the machine running the Teleport Database Service.
When running on EKS, this error may occur if the Teleport Database Service cannot access IMDSv2 when the PUT requests hop limit on the worker node instance is set to 1. You can use the following commands to check the hop limit:
$ aws ec2 describe-instances --instance-ids <node-instance-id> | grep HttpPutResponseHopLimit
"HttpPutResponseHopLimit": 1,
See IMDSv2 support for EKS and EKS best practices for more details.
Timeout errors
The Teleport Database Service needs connectivity to your database endpoints. That may require
enabling inbound traffic on the database from the Database Service on the same VPC or routing rules from another VPC. Using the nc
program you can verify connections to databases:
$ nc -zv postgres-instance-1.sadas.us-east-1.rds.amazonaws.com 5432
# Connection to postgres-instance-1.sadas.us-east-1.rds.amazonaws.com (172.31.24.172) 5432 port [tcp/postgresql] succeeded!
Not authorized to perform sts:AssumeRole
The Database Service assumes an IAM role in one of following situations:
- An IAM role is used as
db_userwhen accessing AWS services that require IAM roles as database users, such as DynamoDB, Keyspaces, Opensearch, and Redshift Serverless. - The
assume_role_arnfield is specified for the database resources or dynamic resource matchers.
Role chaining
When both of the above conditions are true for a database connection, the
Database Service performs a role chaining by assuming the IAM role specified
assume_role_arn first then using that IAM role to assume the IAM role for
db_user.
You may encounter the following error if the trust relationship is not configured properly between the IAM roles:
AccessDenied: User: arn:aws:sts::111111111111:assumed-role/database-service-role/i-* is not authorized to perform: sts:AssumeRole on resource: arn:aws:iam::111111111111:role/database-user-role
To allow IAM Role role1 to assume IAM Role role2, the following is
generally required:
1. Configure Trust Relationships on role2
role1 or its AWS account should be set as Principal in role2's trust
policy.
- Role as principal
- Account as principal
- Cross-account with external-id
{
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Principal": {
"AWS": "arn:aws:iam::aws-account-id:role/role1"
},
"Action": "sts:AssumeRole"
}
]
}
{
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Principal": {
"AWS": "arn:aws:iam::aws-account-id:root"
},
"Action": "sts:AssumeRole"
}
]
}
{
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Principal": {
"AWS": "arn:aws:iam::external-aws-account-id:role/role1"
},
"Action": "sts:AssumeRole",
"Condition": {
"StringEquals": {
"sts:ExternalId": "example-external-id"
}
}
}
]
}
2. Configure Permissions Policies on role1
role1 requires sts:AssumeRole permissions, for example:
{
"Version": "2012-10-17",
"Statement": [
{
"Action": "sts:AssumeRole",
"Effect": "Allow",
"Resource": "arn:aws:iam::aws-account-id:role/role2"
}
]
}
Note that this policy can be omitted when role1 and role2 are in the same
AWS account and role1's full ARN is configured as Principal in role2's
trust policy.
3. Configure Permissions Boundary on role1
role1 also requires sts:AssumeRole permissions in its boundary policy, for
example:
{
"Version": "2012-10-17",
"Statement": [
{
"Action": "sts:AssumeRole",
"Effect": "Allow",
"Resource": "*"
}
]
}
Note that this is only required when a boundary policy is attached to role1.
You can test the trust relationship by running this AWS CLI command as role1:
aws sts assume-role --role-arn arn:aws:iam::111111111111:role/role2 --role-session-name test-trust-relationship
Learn more on how to use trust policies with IAM roles.
Maximum policy size exceeded errors
Due to IAM and STS character limits, you may encounter one of the following errors in the Database Service logs when large numbers of databases are registered:
LimitExceeded: Maximum policy size of 2048 bytes exceeded for user <iam-user>LimitExceeded: Maximum policy size of 10240 bytes exceeded for role <iam-role>
For reference, a user policy can maintain permissions for approximately 6 Redshift databases, or 20 RDS databases due to the IAM policy character limits. A role policy can maintain permissions for approximately 30 Redshift databases, or 100 RDS databases.
To get around this limit, try using one or a combination of the following methods:
Method 1: Organize IAM roles with "assume_role_arn"
You can reduce the policy size by separating them into multiple IAM roles. Use
assume_role_arn to specify different IAM roles for accessing the databases:
- Auto-Discovery by Discovery Service
- Auto-Discovery by Database Service
- Static config
- Other dynamic resources
You can specify assume_role_arn in the AWS matchers of Discovery Service's
configuration:
discovery_service:
enabled: "yes"
aws:
- types: ["rds"]
regions: ["us-west-1", "us-west-2"]
assume_role_arn: "arn:aws:iam::123456789012:role/example-role-rds-env-prod-discovery"
tags:
"env": "prod"
- types: ["redshift", "redshift-serverless"]
regions: ["us-west-2"]
assume_role_arn: "arn:aws:iam::123456789012:role/example-role-redshift-env-dev"
tags:
"env": "dev"
The Discovery Service will use the IAM roles specified in assume_role_arn
for discovery, and by default the Database Service will use the same IAM
roles for authentication.
However, you can also overwrite the IAM roles for authentication by Database Service if you wish to use different roles:
db_service:
enabled: "yes"
resources:
# Matches us-west-1 env=prod RDS databases from Discovery Service, and
# overwrites assume_role_arn.
- labels:
"env": "prod"
"region": "us-west-1"
aws:
assume_role_arn: "arn:aws:iam::123456789012:role/example-role-rds-env-prod-us-west-1-access"
# Matches us-west-2 env=prod RDS databases from Discovery Service, and
# overwrites assume_role_arn.
- labels:
"env": "prod"
"region": "us-west-2"
aws:
assume_role_arn: "arn:aws:iam::123456789012:role/example-role-rds-env-prod-us-west-2-access"
# Matches env=dev Redshift databases from Discovery Service and inherits
# "arn:aws:iam::123456789012:role/example-role-redshift-env-dev"
- labels:
"env": "dev"
Teleport generates certain labels derived from the cloud resource attributes during discovery. See Auto-Discovery labels /labels/#auto-discovery) for more details.
Create or print the required IAM policies with the following commands and attach them to the respective IAM roles:
$ teleport db configure aws create-iam --types redshift,redshift-serverless --name teleport-redshift-access
$ teleport db configure aws print-iam --types redshift,redshift-serverless
Refer to the command usage for a complete list of database types supported by
the --types option.
You can specify assume_role_arn in the AWS matchers of Database Service's
configuration:
db_service:
enabled: "yes"
aws:
- types: ["rds"]
regions: ["us-west-1", "us-west-2"]
assume_role_arn: "arn:aws:iam::123456789012:role/example-role-rds-env-prod"
tags:
"env": "prod"
- types: ["redshift", "redshift-serverless"]
regions: ["us-west-2"]
assume_role_arn: "arn:aws:iam::123456789012:role/example-role-redshift-env-dev"
tags:
"env": "dev"
The Database Service will use the IAM roles specified assume_role_arn for
both discovery and authentication.
To bootstrap IAM permissions, run the bootstrap command for each assume_role_arn:
$ teleport db configure bootstrap \
-c /etc/teleport.yaml \
--policy-name teleport-policy-rds-env-prod \
--attach-to-role "arn:aws:iam::123456789012:role/example-role-rds-env-prod"
You can specify aws.assume_role_arn when defining databases in Database
Service's configuration:
db_service:
enabled: "yes"
databases:
- name: "rds-postgres"
protocol: "postgres"
uri: "rds-postgres.abcdef012345.us-west-1.rds.amazonaws.com:5432"
aws:
assume_role_arn: "arn:aws:iam::123456789012:role/example-rds-access-role"
To bootstrap IAM permissions, run the bootstrap command for each assume_role_arn:
$ teleport db configure bootstrap \
-c /etc/teleport.yaml \
--policy-name teleport-policy-rds-access \
--attach-to-role "arn:aws:iam::123456789012:role/example-rds-access-role"
You can specify aws.assume_role_arn when defining databases:
kind: db
version: v3
metadata:
name: "rds-postgres"
labels:
env: "dev"
spec:
protocol: "postgres"
uri: "rds-postgres.abcdef012345.us-west-1.rds.amazonaws.com:5432"
aws:
assume_role_arn: "arn:aws:iam::123456789012:role/example-rds-access-role"
Alternatively, you can overwrite the IAM roles for authentication by Database Service:
db_service:
enabled: "yes"
resources:
# Matches env=dev databases and overwrites assume_role_arn.
- labels:
"env": "dev"
aws:
assume_role_arn: "arn:aws:iam::123456789012:role/example-env-dev-access"
# Matches env=prod database, and use the assume_role_arn in the database's
# definition or use the host IAM identity if assume_role_arn is empty.
- labels:
"env": "prod"
Create or print the required IAM policies with the following commands and attach them to the respective IAM roles:
$ teleport db configure aws create-iam --types rds --name teleport-rds-access
$ teleport db configure aws print-iam --types rds
Refer to the command usage for a complete list of database types supported by
the --types option.
The IAM roles specified in assume_role_arn must
trust
the IAM identity of the host running the Database Service.
The assume_role_arn is not limited to the same AWS account so you can also
use this feature for AWS Cross-Account
Access.
Method 2: Manually manage your IAM policies
You can manually manage IAM policies for database connections instead of relying on the Database Service to update them.
For example, you can limit the character size by attaching a policy with a wildcard "*" for "Resource":
- RDS or RDS Proxy
- Redshift
{
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Action": "rds-db:connect",
"Resource": "*"
}
]
}
{
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Action": "redshift:GetClusterCredentials",
"Resource": "*"
}
]
}
You can safely remove the inline policy created by the Database Service and the
IAM permissions for the Database Service to Get/Put/Delete the user or role
policy.
Method 3: Separate Database Services
You can deploy the Database Service in a highly available (HA) configuration where databases can be sharded to separate Database Services with different IAM roles.
Method 4: Use IAM roles instead of IAM users
IAM users have a lower character limit compared to IAM roles. If the limit is exceeded for a user policy, it is recommended to use IAM roles for the Database Service instead.
Next steps
- Learn how to restrict access to certain users and databases.
- View the High Availability (HA) guide.
- Take a look at the YAML configuration reference.
- See the full CLI reference.
- Learn more on Setting up database credentials in AWS Secrets Manager and Setting up AWS Identity and Access Management (IAM) policies for RDS Proxy